Interface DelAdminMgr
-
- All Superinterfaces:
Manageable
- All Known Implementing Classes:
DelAdminMgrImpl,DelAdminMgrRestImpl
public interface DelAdminMgr extends Manageable
This class prescribes the ARBAC02 DelAdminMgr interface for performing policy administration of Fortress ARBAC entities that reside in LDAP directory. These APIs map directly to similar named APIs specified by ARBAC02 functions. The ARBAC Functional specification describes delegated administrative operations for the creation and maintenance of ARBAC element sets and relations. Delegated administrative review functions for performing administrative queries and system functions for creating and managing ARBAC attributes on user sessions and making delegated administrative access control decisions.Administrative Role Based Access Control (ARBAC)
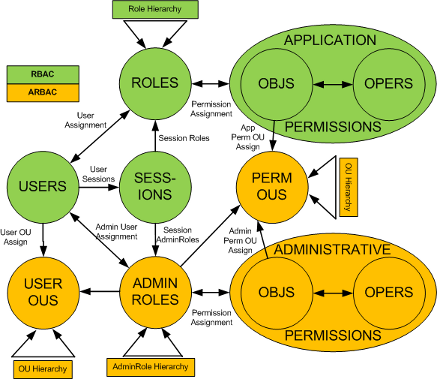
Fortress fully supports the Oh/Sandhu/Zhang ARBAC02 model for delegated administration. ARBAC provides large enterprises the capability to delegate administrative authority to users that reside outside of the security admin group. Decentralizing administration helps because it provides security provisioning capability to work groups without sacrificing regulations for accountability or traceability.
This interface's implementer will NOT be thread safe if parent instance variables (
Manageable.setContextId(String)orManageable.setAdmin(org.apache.directory.fortress.core.model.Session)) are set.- Author:
- Apache Directory Project
-
-
Method Summary
All Methods Instance Methods Abstract Methods Modifier and Type Method Description OrgUnitadd(OrgUnit entity)Commands adds a new OrgUnit entity to OrgUnit dataset.voidaddAscendant(AdminRole childRole, AdminRole parentRole)This command creates a new role parentRole, and inserts it in the role hierarchy as an immediate ascendant of the existing role childRole.voidaddAscendant(OrgUnit child, OrgUnit parent)This command creates a new orgunit parent, and inserts it in the orgunit hierarchy as an immediate ascendant of the existing child orgunit.voidaddDescendant(AdminRole parentRole, AdminRole childRole)This command creates a new role childRole, and inserts it in the role hierarchy as an immediate descendant of the existing role parentRole.voidaddDescendant(OrgUnit parent, OrgUnit child)This command creates a new orgunit child, and inserts it in the orgunit hierarchy as an immediate descendant of the existing orgunit parent.voidaddInheritance(AdminRole parentRole, AdminRole childRole)This command establishes a new immediate inheritance relationship parentRole <<-- childRole between existing roles parentRole, childRole.voidaddInheritance(OrgUnit parent, OrgUnit child)This command establishes a new immediate inheritance relationship with parent orgunit <<-- child orgunitPermissionaddPermission(Permission perm)This method will add an administrative permission operation to an existing permission object which resides underou=AdminPerms,ou=ARBAC,dc=yourHostName,dc=comcontainer in directory information tree.PermObjaddPermObj(PermObj pObj)This method will add administrative permission object to admin perms container in directory.AdminRoleaddRole(AdminRole role)This command creates a new admin role.voidassignUser(UserAdminRole uAdminRole)This command assigns a user to an admin role.voiddeassignUser(UserAdminRole uAdminRole)This method removes assigned admin role from user entity.OrgUnitdelete(OrgUnit entity)Commands deletes existing OrgUnit entity to OrgUnit dataset.voiddeleteInheritance(AdminRole parentRole, AdminRole childRole)This command deletes an existing immediate inheritance relationship parentRole <<-- childRole.voiddeleteInheritance(OrgUnit parent, OrgUnit child)This command deletes an existing immediate inheritance relationship parent <<-- child.voiddeletePermission(Permission perm)This method will remove administrative permission operation entity from permission object.voiddeletePermObj(PermObj pObj)This method will remove administrative permission object from perms container in directory.voiddeleteRole(AdminRole role)This command deletes an existing admin role from the ARBAC database.voidgrantPermission(Permission perm, AdminRole role)This command grants an AdminRole the administrative permission to perform an operation on an object to a role.voidgrantPermission(Permission perm, User user)This command grants a user the administrative permission to perform an operation on an object to a user.voidrevokePermission(Permission perm, AdminRole role)This command revokes the administrative permission to perform an operation on an object from the set of permissions assigned to an AdminRole.voidrevokePermission(Permission perm, User user)This command revokes the administrative permission to perform an operation on an object from the set of permissions assigned to a user.OrgUnitupdate(OrgUnit entity)Commands updates existing OrgUnit entity to OrgUnit dataset.PermissionupdatePermission(Permission perm)This method will update administrative permission operation pre-existing in target directory underou=AdminPerms,ou=ARBAC,dc=yourHostName,dc=comcontainer in directory information tree.PermObjupdatePermObj(PermObj pObj)This method will update administrative permission object in perms container in directory.AdminRoleupdateRole(AdminRole role)Method will update an AdminRole entity in the directory.-
Methods inherited from interface org.apache.directory.fortress.core.Manageable
setAdmin, setContextId
-
-
-
-
Method Detail
-
addRole
AdminRole addRole(AdminRole role) throws SecurityException
This command creates a new admin role. The command is valid if and only if the new admin role is not already a member of the ADMIN ROLES data set. The ADMIN ROLES data set is updated. Initially, no user or permission is assigned to the new role.required parameters
Role.name- contains the name of the new AdminRole being targeted for addition to LDAP
optional parameters
Role.description- contains any safe textAdminRole.osPs* - multivalued attribute used to set associations to existing PERMS OrgUnitsAdminRole.osUs* - multivalued attribute used to set associations to existing USERS OrgUnits-
AdminRole.beginRange- contains the name of an existing RBAC Role that represents the lowest role in hierarchy that administrator (whoever has this AdminRole activated) controls -
AdminRole.endRange- contains the name of an existing RBAC Role that represents that highest role in hierarchy that administrator may control -
AdminRole.beginInclusive- if 'true' the RBAC Role specified in beginRange is also controlled by the possessor of this AdminRole -
AdminRole.endInclusive- if 'true' the RBAC Role specified in endRange is also controlled by the administrator -
Role.beginTime- HHMM - determines begin hour adminRole may be activated into user's ARBAC session -
Role.endTime- HHMM - determines end hour adminRole may be activated into user's ARBAC session. -
Role.beginDate- YYYYMMDD - determines date when adminRole may be activated into user's ARBAC session -
Role.endDate- YYYYMMDD - indicates latest date adminRole may be activated into user's ARBAC session Role.beginLockDate- YYYYMMDD - determines beginning of enforced inactive statusRole.endLockDate- YYYYMMDD - determines end of enforced inactive statusRole.dayMask- 1234567, 1 = Sunday, 2 = Monday, etc - specifies which day role may be activated into user's ARBAC session
- Parameters:
role- Contains role name and description.- Returns:
- AdminRole contains reference to entity added.
- Throws:
SecurityException- thrown in the event of data validation or system error.
-
deleteRole
void deleteRole(AdminRole role) throws SecurityException
This command deletes an existing admin role from the ARBAC database. The command is valid if and only if the role to be deleted is a member of the ADMIN ROLES data set. This command will also deassign role from all users.required parameters
Role.name- contains the name of the new AdminRole being targeted for removal
- Parameters:
role- Contains role name.- Throws:
SecurityException- Thrown in the event of data validation or system error.
-
updateRole
AdminRole updateRole(AdminRole role) throws SecurityException
Method will update an AdminRole entity in the directory. The role must exist in directory prior to this call.required parameters
Role.name- contains the name of the new AdminRole being targeted for updating
optional parameters
Role.description- contains any safe textAdminRole.osPs* - multivalued attribute used to set associations to existing PERMS OrgUnitsAdminRole.osUs* - multivalued attribute used to set associations to existing USERS OrgUnits-
AdminRole.beginRange- contains the name of an existing RBAC Role that represents the lowest role in hierarchy that administrator (whoever has this AdminRole activated) controls -
AdminRole.endRange- contains the name of an existing RBAC Role that represents that highest role in hierarchy that administrator may control -
AdminRole.beginInclusive- if 'true' the RBAC Role specified in beginRange is also controlled by the possessor of this AdminRole -
AdminRole.endInclusive- if 'true' the RBAC Role specified in endRange is also controlled by the administrator -
Role.beginTime- HHMM - determines begin hour adminRole may be activated into user's ARBAC session -
Role.endTime- HHMM - determines end hour adminRole may be activated into user's ARBAC session. -
Role.beginDate- YYYYMMDD - determines date when adminRole may be activated into user's ARBAC session -
Role.endDate- YYYYMMDD - indicates latest date adminRole may be activated into user's ARBAC session Role.beginLockDate- YYYYMMDD - determines beginning of enforced inactive statusRole.endLockDate- YYYYMMDD - determines end of enforced inactive status-
Role.dayMask- 1234567, 1 = Sunday, 2 = Monday, etc - specifies which day role may be activated into user's ARBAC session
- Parameters:
role- Contains role name and new description.- Returns:
- AdminRole contains reference to entity operated on.
- Throws:
SecurityException- Thrown in the event of data validation or system error.
-
assignUser
void assignUser(UserAdminRole uAdminRole) throws SecurityException
This command assigns a user to an admin role. Successful completion of this op, the following occurs:- User entity (resides in people container) has role assignment added to aux object class attached to actual user record.
- AdminRole entity (resides in admin role container) has userId added as role occupant.
- (optional) Temporal constraints may be associated with
ftUserAttrsaux object class based on:- timeout - number (in minutes) of session inactivity time allowed.
- beginDate - YYYYMMDD - determines date when role may be activated.
- endDate - YYMMDD - indicates latest date role may be activated.
- beginLockDate - YYYYMMDD - determines beginning of enforced inactive status
- endLockDate - YYMMDD - determines end of enforced inactive status.
- beginTime - HHMM - determines begin hour role may be activated in user's session.
- endTime - HHMM - determines end hour role may be activated in user's session.*
- dayMask - 1234567, 1 = Sunday, 2 = Monday, etc - specifies which day of week role may be activated.
required parameters
UserRole.name- contains the name for already existing AdminRole to be assignedUserRole.userId- contains the userId for existing User
optional parameters
-
UserRole.beginTime- HHMM - determines begin hour AdminRole may be activated into user's RBAC session -
UserRole.endTime- HHMM - determines end hour AdminRole may be activated into user's RBAC session. -
UserRole.beginDate- YYYYMMDD - determines date when AdminRole may be activated into user's RBAC session -
UserRole.endDate- YYYYMMDD - indicates latest date AdminRole may be activated into user's RBAC session UserRole.beginLockDate- YYYYMMDD - determines beginning of enforced inactive statusUserRole.endLockDate- YYYYMMDD - determines end of enforced inactive status-
UserRole.dayMask- 1234567, 1 = Sunday, 2 = Monday, etc - specifies which day role may be activated into user's ARBAC session
- Parameters:
uAdminRole- entity containsUser.userIdandRole.nameand optionalConstraints..- Throws:
SecurityException- in the event data error in user or role objects or system error.
-
deassignUser
void deassignUser(UserAdminRole uAdminRole) throws SecurityException
This method removes assigned admin role from user entity. Both user and admin role entities must exist and have role relationship before calling this method. Successful completion:del Role to User assignment in User data set AND User to Role assignment in Admin Role data set.
required parameters
-
UserRole.name- contains the name for already existing AdminRole to be deassigned -
UserRole.userId- contains the userId for existing User
- Parameters:
uAdminRole- entity containsUser.userIdandRole.name.- Throws:
SecurityException- - in the event data error in user or role objects or system error.
-
-
add
OrgUnit add(OrgUnit entity) throws SecurityException
Commands adds a new OrgUnit entity to OrgUnit dataset. The OrgUnit can be either User or Perm and is set by setting type attribute.required parameters
-
OrgUnit.name- contains the name of new USERS or PERMS OrgUnit to be added -
OrgUnit.type- contains the type of OU:OrgUnit.Type.USERorOrgUnit.Type.PERM
optional parameters
OrgUnit.description- contains any safe text
- Parameters:
entity- contains OrgUnit name and type.- Returns:
- OrgUnit contains reference to entity added.
- Throws:
SecurityException- in the event of data validation or system error.
-
-
update
OrgUnit update(OrgUnit entity) throws SecurityException
Commands updates existing OrgUnit entity to OrgUnit dataset. The OrgUnit can be either User or Perm and is set by setting type attribute.required parameters
-
OrgUnit.name- contains the name of new USERS or PERMS OrgUnit to be updated -
OrgUnit.type- contains the type of OU:OrgUnit.Type.USERorOrgUnit.Type.PERM
optional parameters
OrgUnit.description- contains any safe text
- Parameters:
entity- contains OrgUnit name and type.- Returns:
- OrgUnit contains reference to entity operated on.
- Throws:
SecurityException- in the event of data validation or system error.
-
-
delete
OrgUnit delete(OrgUnit entity) throws SecurityException
Commands deletes existing OrgUnit entity to OrgUnit dataset. The OrgUnit can be either User or Perm and is set by setting type attribute.required parameters
-
OrgUnit.name- contains the name of new USERS or PERMS OrgUnit to be removed -
OrgUnit.type- contains the type of OU:OrgUnit.Type.USERorOrgUnit.Type.PERM
- Parameters:
entity- contains OrgUnit name and type.- Returns:
- OrgUnit contains reference to entity operated on.
- Throws:
SecurityException- in the event of data validation or system error.
-
-
addDescendant
void addDescendant(OrgUnit parent, OrgUnit child) throws SecurityException
This command creates a new orgunit child, and inserts it in the orgunit hierarchy as an immediate descendant of the existing orgunit parent.The command is valid if and only if:
- The child orgunit is not a member of the ORGUNITS data set.
- The parent orgunit is a member of the ORGUNITS data set.
This method:
- Adds new orgunit.
- Assigns orgunit relationship between new child and pre-existing parent.
required parameters
-
parentRole -
OrgUnit.name- contains the name of existing OrgUnit to be parent -
parentRole -
OrgUnit.type- contains the type of OrgUnit targeted:OrgUnit.Type.USERorOrgUnit.Type.PERM -
childRole -
OrgUnit.name- contains the name of new OrgUnit to be child
optional parameters child
-
childRole -
OrgUnit.description- maps to description attribute on organizationalUnit object class for new child
- Parameters:
parent- This entity must be present in ORGUNIT data set. Success will add rel with child.child- This entity must not be present in ORGUNIT data set. Success will add the new entity to ORGUNIT data set.- Throws:
SecurityException- thrown in the event of data validation or system error.
-
addAscendant
void addAscendant(OrgUnit child, OrgUnit parent) throws SecurityException
This command creates a new orgunit parent, and inserts it in the orgunit hierarchy as an immediate ascendant of the existing child orgunit.The command is valid if and only if:
- The parent is not a member of the ORGUNITS data set.
- The child is a member of the ORGUNITS data set.
This method:
- Adds new orgunit.
- Assigns orgunit relationship between new parent and pre-existing child.
required parameters
-
child -
OrgUnit.name- contains the name of existing OrgUnit to be parent -
parent -
OrgUnit.type- contains the type of OrgUnit targeted:OrgUnit.Type.USERorOrgUnit.Type.PERM -
parent -
OrgUnit.name- contains the name of new OrgUnit to be child
optional parameters child
-
parent -
OrgUnit.description- maps to description attribute on organizationalUnit object class for new child
- Parameters:
parent- completion of op assigns new child relationship with child orgunit.child- completion of op assigns new parent relationship with parent orgunit.- Throws:
SecurityException- thrown in the event of data validation or system error.
-
addInheritance
void addInheritance(OrgUnit parent, OrgUnit child) throws SecurityException
This command establishes a new immediate inheritance relationship with parent orgunit <<-- child orgunitThe command is valid if and only if:
- The parent and child are members of the ORGUNITS data set.
- The parent is not an immediate ascendant of child.
- The child does not properly inherit parent (in order to avoid cycle creation).
required parameters
-
parent -
OrgUnit.name- contains the name of existing OrgUnit to be parent -
parent -
OrgUnit.type- contains the type of OrgUnit targeted:OrgUnit.Type.USERorOrgUnit.Type.PERM -
child -
OrgUnit.name- contains the name of existing OrgUnit to be child
- Parameters:
parent- completion of op deassigns child relationship with child orgunit.child- completion of op deassigns parent relationship with parent orgunit.- Throws:
SecurityException- thrown in the event of data validation or system error.
-
deleteInheritance
void deleteInheritance(OrgUnit parent, OrgUnit child) throws SecurityException
This command deletes an existing immediate inheritance relationship parent <<-- child.The command is valid if and only if:
- The orgunits parent and child are members of the ORGUNITS data set.
- The parent is an immediate ascendant of child.
- The new inheritance relation is computed as the reflexive-transitive closure of the immediate inheritance relation resulted after deleting the relationship parent <<-- child.
required parameters
-
parent -
OrgUnit.name- contains the name of existing OrgUnit to remove as parent -
parent -
OrgUnit.type- contains the type of OrgUnit targeted:OrgUnit.Type.USERorOrgUnit.Type.PERM -
child -
OrgUnit.name- contains the name of existing OrgUnit to remove as child
- Parameters:
parent- completion of op removes child relationship with childRole.child- completion of op removes parent relationship with parentRole.- Throws:
SecurityException- thrown in the event of data validation or system error.
-
addDescendant
void addDescendant(AdminRole parentRole, AdminRole childRole) throws SecurityException
This command creates a new role childRole, and inserts it in the role hierarchy as an immediate descendant of the existing role parentRole. The command is valid if and only if childRole is not a member of the ADMINROLES data set, and parentRole is a member of the ADMINROLES data set.This method:
- Adds new role.
- Assigns role relationship between new childRole and pre-existing parentRole.
required parameters
-
parentRole -
Role.name- contains the name of existing Role to be parent -
childRole -
Role.name- contains the name of new Role to be child
optional parameters childRole
-
childRole -
Role.description- maps to description attribute on organizationalRole object class for new child -
childRole -
Role.beginTime- HHMM - determines begin hour role may be activated into user's session for new child -
childRole -
Role.endTime- HHMM - determines end hour role may be activated into user's session for new child -
childRole -
Role.beginDate- YYYYMMDD - determines date when role may be activated into user's session for new child -
childRole -
Role.endDate- YYYYMMDD - indicates latest date role may be activated into user's session for new chil -
childRole -
Role.beginLockDate- YYYYMMDD - determines beginning of enforced inactive status for new child -
childRole -
Role.endLockDate- YYYYMMDD - determines end of enforced inactive status for new child -
childRole -
Role.dayMask- 1234567, 1 = Sunday, 2 = Monday, etc - specifies which day role may be activated into user's session for new child
- Parameters:
parentRole- This entity must be present in ADMINROLES data set. Success will add role rel with childRole.childRole- This entity must not be present in ADMINROLES data set. Success will add the new role entity to ADMINROLES data set.- Throws:
SecurityException- thrown in the event of data validation or system error.
-
addAscendant
void addAscendant(AdminRole childRole, AdminRole parentRole) throws SecurityException
This command creates a new role parentRole, and inserts it in the role hierarchy as an immediate ascendant of the existing role childRole. The command is valid if and only if parentRole is not a member of the ADMINROLES data set, and childRole is a member of the ADMINROLES data set. This method:- Adds new role.
- Assigns role relationship between new parentRole and pre-existing childRole.
required parameters
-
childRole -
Role.name- contains the name of existing Role to be child -
parentRole -
Role.name- contains the name of new Role to be added as parent
optional parameters parentRole
-
parentRole -
Role.description- maps to description attribute on organizationalRole object class for new parent -
parentRole -
Role.beginTime- HHMM - determines begin hour role may be activated into user's session for new parent -
parentRole -
Role.endTime- HHMM - determines end hour role may be activated into user's session for new parent -
parentRole -
Role.beginDate- YYYYMMDD - determines date when role may be activated into user's session for new parent -
parentRole -
Role.endDate- YYYYMMDD - indicates latest date role may be activated into user's session for new parent -
parentRole -
Role.beginLockDate- YYYYMMDD - determines beginning of enforced inactive status for new parent -
parentRole -
Role.endLockDate- YYYYMMDD - determines end of enforced inactive status for new parent -
parentRole -
Role.dayMask- 1234567, 1 = Sunday, 2 = Monday, etc - specifies which day role may be activated into user's session for new parent
- Parameters:
parentRole- completion of op assigns new child relationship with childRole.childRole- completion of op assigns new parent relationship with parentRole.- Throws:
SecurityException- thrown in the event of data validation or system error.
-
addInheritance
void addInheritance(AdminRole parentRole, AdminRole childRole) throws SecurityException
This command establishes a new immediate inheritance relationship parentRole <<-- childRole between existing roles parentRole, childRole. The command is valid if and only if parentRole and childRole are members of the ADMINROLES data set, parentRole is not an immediate ascendant of childRole, and childRole does not properly inherit parentRole (in order to avoid cycle creation).required parameters
- Parameters:
parentRole- completion of op deassigns child relationship with childRole.childRole- completion of op deassigns parent relationship with parentRole.- Throws:
SecurityException- thrown in the event of data validation or system error.
-
deleteInheritance
void deleteInheritance(AdminRole parentRole, AdminRole childRole) throws SecurityException
This command deletes an existing immediate inheritance relationship parentRole <<-- childRole. The command is valid if and only if the roles parentRole and childRole are members of the ADMINROLES data set, and parentRole is an immediate ascendant of childRole. The new inheritance relation is computed as the reflexive-transitive closure of the immediate inheritance relation resulted after deleting the relationship parentRole <<-- childRole.required parameters
- Parameters:
parentRole- completion of op removes child relationship with childRole.childRole- completion of op removes parent relationship with parentRole.- Throws:
SecurityException- thrown in the event of data validation or system error.
-
addPermission
Permission addPermission(Permission perm) throws SecurityException
This method will add an administrative permission operation to an existing permission object which resides underou=AdminPerms,ou=ARBAC,dc=yourHostName,dc=comcontainer in directory information tree. The perm operation entity may haveAdminRoleorUserassociations. The targetPermissionmust not exist prior to calling. A Fortress Permission instance exists in a hierarchical, one-many relationship between its parent and itself as stored in ldap tree: (PermObj*->Permission).required parameters
-
Permission.objName- contains the name of existing object being targeted for the permission add -
Permission.opName- contains the name of new permission operation being added
optional parameters
-
Permission.roles* - multi occurring attribute contains RBAC Roles that permission operation is being granted to -
Permission.users* - multi occurring attribute contains Users that permission operation is being granted to -
Permission.props* - multi-occurring property key and values are separated with a ':'. e.g. mykey1:myvalue1 -
Permission.type- any safe text
- Parameters:
perm- must contain the object,Permission.objName, and operation,Permission.opName, that identifies target along with optional other attributes..- Returns:
- copy of Permission entity.
- Throws:
SecurityException- - thrown in the event of perm object data or system error.
-
-
updatePermission
Permission updatePermission(Permission perm) throws SecurityException
This method will update administrative permission operation pre-existing in target directory underou=AdminPerms,ou=ARBAC,dc=yourHostName,dc=comcontainer in directory information tree. The perm operation entity may also containAdminRoleorUserassociations to add or remove using this function. The perm operation must exist before making this call. Only non-null attributes will be updated.required parameters
-
Permission.objName- contains the name of existing object being targeted for the permission update -
Permission.opName- contains the name of existing permission operation being updated
optional parameters
-
Permission.roles* - multi occurring attribute contains RBAC Roles that permission operation is being granted to -
Permission.users* - multi occurring attribute contains Users that permission operation is being granted to -
Permission.props* - multi-occurring property key and values are separated with a ':'. e.g. mykey1:myvalue1 Permission.type- any safe text
- Parameters:
perm- must contain the object,Permission.objName, and operation,Permission.opName, that identifies target and any optional data to update. Null or empty attributes will be ignored.- Returns:
- copy of Permission entity.
- Throws:
SecurityException- thrown in the event of perm object data or system error.
-
-
deletePermission
void deletePermission(Permission perm) throws SecurityException
This method will remove administrative permission operation entity from permission object. A Fortress permission is (object->operation). The perm operation must exist before making this call.required parameters
-
Permission.objName- contains the name of existing object being targeted for the permission delete -
Permission.opName- contains the name of existing permission operation being removed
- Parameters:
perm- must contain the object,Permission.objName, and operation,Permission.opName, that identifies target.- Throws:
SecurityException- thrown in the event of perm object data or system error.
-
-
addPermObj
PermObj addPermObj(PermObj pObj) throws SecurityException
This method will add administrative permission object to admin perms container in directory. The perm object must not exist before making this call. APermObjinstance exists in a hierarchical, one-many relationship between itself and children as stored in ldap tree: (PermObj* ->Permission).required parameters
-
PermObj.objName- contains the name of new object being added -
PermObj.ou- contains the name of an existing PERMS OrgUnit this object is associated with
optional parameters
PermObj.description- any safe textPermObj.type- contains any safe text-
PermObj.props* - multi-occurring property key and values are separated with a ':'. e.g. mykey1:myvalue1
- Parameters:
pObj- must contain thePermObj.objNameandPermObj.ou. The other attributes are optional.- Returns:
- copy of PermObj entity.
- Throws:
SecurityException- - thrown in the event of perm object data or system error.
-
-
updatePermObj
PermObj updatePermObj(PermObj pObj) throws SecurityException
This method will update administrative permission object in perms container in directory. The perm object must exist before making this call. APermObjinstance exists in a hierarchical, one-many relationship between itself and children as stored in ldap tree: (PermObj* ->Permission).required parameters
-
PermObj.objName- contains the name of existing object being updated
optional parameters
-
PermObj.ou- contains the name of an existing PERMS OrgUnit this object is associated with PermObj.description- any safe textPermObj.type- contains any safe text-
PermObj.props* - multi-occurring property key and values are separated with a ':'. e.g. mykey1:myvalue1
- Parameters:
pObj- must contain thePermObj.objName. Only non-null attributes will be updated.- Returns:
- copy of newly updated PermObj entity.
- Throws:
SecurityException- thrown in the event of perm object data or system error.
-
-
deletePermObj
void deletePermObj(PermObj pObj) throws SecurityException
This method will remove administrative permission object from perms container in directory. This method will also remove in associated permission objects that are attached to this object.required parameters
-
PermObj.objName- contains the name of existing object targeted for removal
- Parameters:
pObj- must contain thePermObj.objNameof object targeted for removal.- Throws:
SecurityException- thrown in the event of perm object data or system error.
-
-
grantPermission
void grantPermission(Permission perm, AdminRole role) throws SecurityException
This command grants an AdminRole the administrative permission to perform an operation on an object to a role. The command is implemented by granting administrative permission by setting the access control list of the object involved. The command is valid if and only if the pair (operation, object) represents a permission, and the adminRole is a member of the ADMIN_ROLES data set.required parameters
Permission.objName- contains the object namePermission.opName- contains the operation nameRole.name- contains the adminRole name
- Parameters:
perm- must contain the object,Permission.objName, and operation,Permission.opName, that identifies target.role- must containsRole.name.- Throws:
SecurityException- Thrown in the event of data validation or system error.
-
revokePermission
void revokePermission(Permission perm, AdminRole role) throws SecurityException
This command revokes the administrative permission to perform an operation on an object from the set of permissions assigned to an AdminRole. The command is implemented by setting the access control list of the object involved. The command is valid if and only if the pair (operation, object) represents a permission, the role is a member of the ADMIN_ROLES data set, and the permission is assigned to that AdminRole.required parameters
Permission.objName- contains the object namePermission.opName- contains the operation nameRole.name- contains the adminRole name
- Parameters:
perm- must contain the object,Permission.objName, and operation,Permission.opName, that identifies target.role- must containsRole.name.- Throws:
SecurityException- Thrown in the event of data validation or system error.
-
grantPermission
void grantPermission(Permission perm, User user) throws SecurityException
This command grants a user the administrative permission to perform an operation on an object to a user. The command is implemented by granting administrative permission by setting the access control list of the object involved. The command is valid if and only if the pair (operation, object) represents an administrative permission, and the user is a member of the USERS data set.required parameters
Permission.objName- contains the object namePermission.opName- contains the operation nameUser.userId- contains the userId
- Parameters:
perm- must contain the object,Permission.objName, and operation,Permission.opName, that identifies target.user- must containUser.userIdof target User entity.- Throws:
SecurityException- Thrown in the event of data validation or system error.
-
revokePermission
void revokePermission(Permission perm, User user) throws SecurityException
This command revokes the administrative permission to perform an operation on an object from the set of permissions assigned to a user. The command is implemented by setting the access control list of the object involved. The command is valid if and only if the pair (operation, object) represents an administrative permission, the user is a member of the USERS data set, and the permission is assigned to that user.required parameters
Permission.objName- contains the object namePermission.opName- contains the operation nameUser.userId- contains the userId
- Parameters:
perm- must contain the object,Permission.objName, and operation,Permission.opName, that identifies target.user- must containUser.userIdof target User entity.- Throws:
SecurityException- Thrown in the event of data validation or system error.
-
-